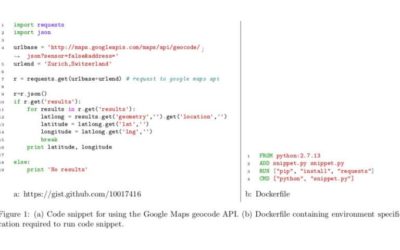
A team of researchers at North Carolina State University has recently carried out an empirical analysis of the executable status of Python code snippets shared on GitHub. Their study, pre-published on arXiv, also presents Gistable, a new database of executable Python...
TECHXPLORE
An intuitive physics model to predict the effects of a collision
Humans have the innate ability to predict the effect of collisions, merely using their common sense. In many cases, humans can even predict the results of similar collisions in situations in which mass, friction, or other factors vary. Could machines also attain a...
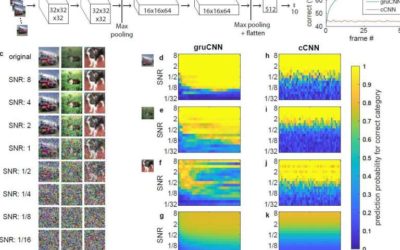
Computer vision in the dark using recurrent CNNs
Over the past few years, classical convolutional neural networks (cCNNs) have led to remarkable advances in computer vision. Many of these algorithms can now categorize objects in good quality images with high accuracy.
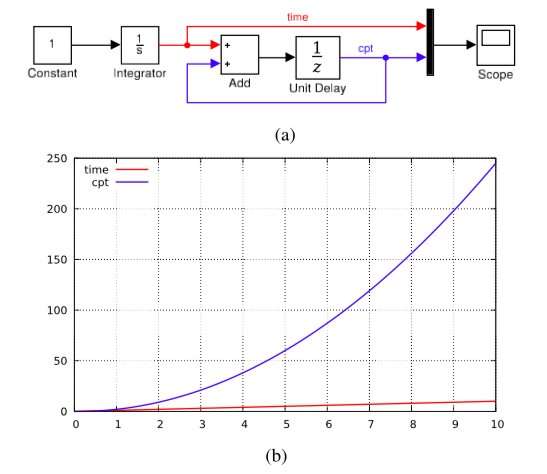
A new approach for designing and implementing a hybrid systems language
Hybrid systems are systems that exhibit both continuous and discrete dynamic behavior, allowing more flexibility in modeling dynamic phenomena. Hybrid systems modeling languages are widely used for the development of cyber-physical systems, in which control software...
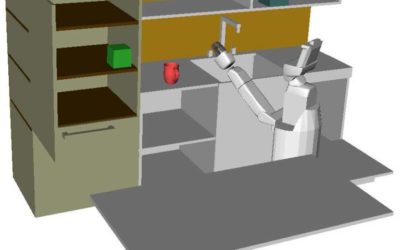
A chance constrained motion planning system for high-dimensional robots
Researchers at MIT's Computer Science and Artificial Intelligence Laboratory have recently developed a chance-constrained motion planning system that can be applied to high degree-of-freedom (DOF) robots under motion uncertainty and in cases of imperfect state...
A conceptual framework for modeling human-robot trust
Researchers at Pennsylvania State University, MIT and Georgia Institute of Technology have recently developed a conceptual framework to model the human-robot trust phenomenon. Their framework, outlined in a paper published on ACM Digital Library, uses computational...
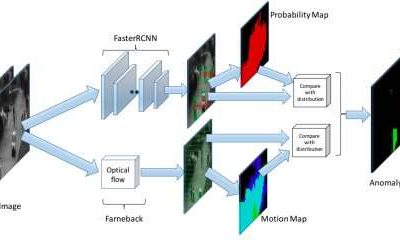
Adaptive anomaly detection in traffic surveillance videos
Researchers at Arizona State University (ASU) have recently developed a new method of detecting unusual activity in traffic surveillance videos, which is based on an adaptive anomaly detection (AAD) framework. Their method, outlined in a paper pre-published on arXiv,...
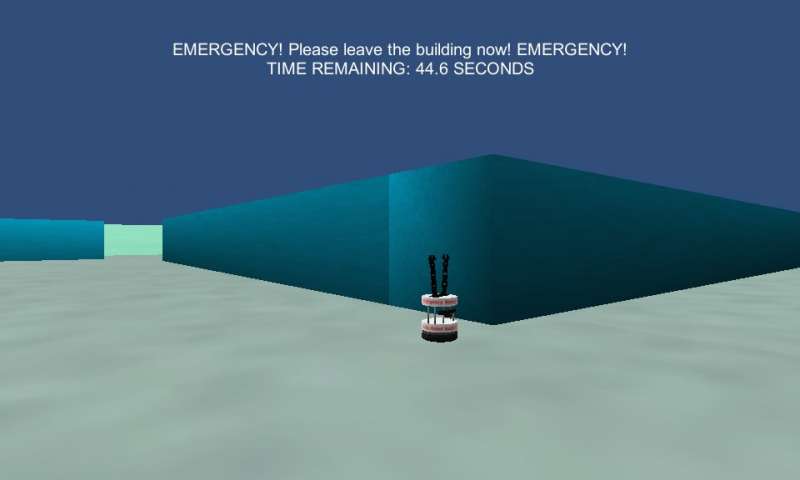
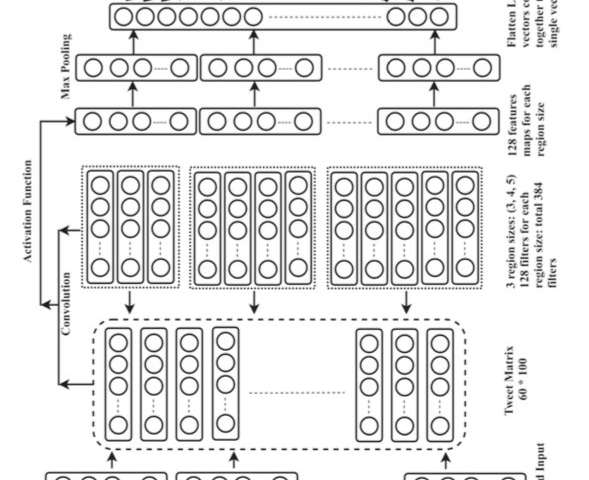
A deep learning approach to identify Twitter users’ location during emergencies
Researchers at the National Institute of Technology Patna, in India, have recently devised a tool to identify the geographical location of emergencies and disasters, as well as that of the people involved in them. Their approach, outlined in a paper in the...
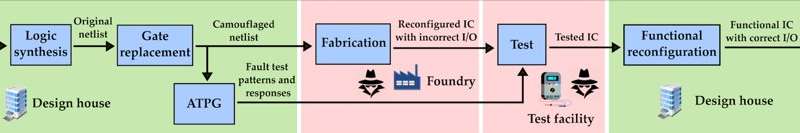
A dynamic camouflaging approach to prevent intellectual property theft
In recent years, hardware-centric security threats have emerged at different stages of the integrated circuit (IC) supply chain. This has enabled the proliferation of various malicious attacks, such as intellectual property (IP) piracy, illegal overproduction of ICs,...
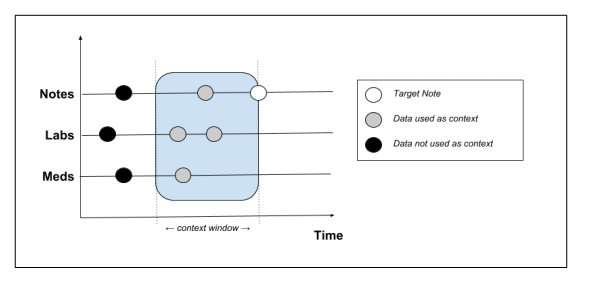
AI-assisted note-taking for electronic health records
Physicians currently spend a lot of time writing notes about patients and inserting them into electronic health record (EHR) systems. According to a 2016 study, doctors spend approximately two hours on administrative work for every hour spent with a patient. Thanks to...